A tool for writing random bytes, encrypting file contents, and hiding encrypted data
Project description
tird
tird (an acronym for "this is random data") is a tool for writing random bytes, encrypting file contents, and hiding encrypted data.
[!NOTE] Further "cryptoblob" implies
tirdencryption format.
Using tird you can:
- Create files with random data. Use them as containers or keyfiles.
- Overwrite the contents of devices and regular files with random data. This can be used to destroy residual data and prepare containers.
- Encrypt file contents and comments with modern cryptographic primitives. The encrypted file format is padded uniform random blob (PURB): it looks like random data and has randomized size. This reduces metadata leakage through file format and length, and also allows cryptoblobs to be hidden among random data.
- Create steganographic (hidden, undetectable) user-driven file systems inside container files and devices. Unlike Veracrypt containers,
tirdcontainers do not contain headers at all: the user specifies the location of the data in the container and is responsible for ensuring that this location is separated from the container. - Resist coercive attacks (keywords: key disclosure law, rubber-hose cryptanalysis).
tirdprovides some forms of plausible deniability out of the box even if you encrypt files without hiding them in containers.
Goals
- Providing protection for individual files, including:
- symmetric encryption;
- reducing metadata leakage;
- hiding encrypted data;
- plausible deniability.
- Providing a stable encryption format with no cryptographic agility for long-term data storage.
- Simplicity and no feature creep: refusal to implement features that are not directly related to primary security goals.
Cryptographic primitives
tird uses the following cryptographic primitives:
BLAKE2(RFC 7693):- salted and personalized
BLAKE2b-512for hashing keyfiles and passphrases; - keyed
BLAKE2b-512for creating message authentication codes; BLAKE2b-256for creating message checksums.
- salted and personalized
Argon2memory-hard function (RFC 9106) for key stretching and key derivation.ChaCha20cipher (RFC 7539) for data encryption.
Encrypted file format
tird encrypted files (cryptoblobs) are indistinguishable from uniform random data and have no identifiable headers. tird produces cryptoblobs contain bilateral randomized padding with uniform random data (PURBs). This minimizes metadata leaks from the file format and makes it possible to hide cryptoblobs among other random data.
Cryptoblob structure:
512 B 0+ B
+——————————+———————————————+
| Comments | File contents |
+——————————+———————————————+
16 B 0+ B | Plaintext/Payload | 64 B 0+ B 16 B
+——————+—————————+——————————————————————————+—————————+—————————+——————+
| Salt | Padding | Ciphertext | MAC tag | Padding | Salt |
+——————+—————————+——————————————————————————+—————————+—————————+——————+
| Random bytes | Random-looking bytes | Random bytes |
+————————————————+————————————————————————————————————+————————————————+
Alternative scheme:
+——————————————————————————————+—————————+
| Salt header: 16 B, 2 parts: | |
| BLAKE2b salt[:8] + | |
| Argon2 salt[:8] | Random |
+——————————————————————————————+ data |
| Randomized padding: 0-20% | |
| of the ciphertext size | |
| by default | |
+——————————————————————————————+—————————+
| Ciphertext: 512+ B consist | |
| of encrypted comments | |
| (always 512 B) and encryped | Random- |
| payload file contents (0+ B) | looking |
+——————————————————————————————+ data |
| MAC tag: 64 B | |
+——————————————————————————————+—————————+
| Randomized padding: 0-20% | |
| of the ciphertext size | |
| by default | Random |
+——————————————————————————————+ data |
| Salt footer: 16 B, 2 parts: | |
| BLAKE2b salt[-8:] + | |
| Argon2 salt[-8:] | |
+——————————————————————————————+—————————+
Hidden user-driven file system and container file format
You can encrypt files and write cryptoblobs over containers starting with arbitary positions. After finishing writing the cryptoblob, you will be asked to remember the location of the cryptoblob in the container (positions of the beginning and end of the cryptoblob), which can be used in the future to extract the cryptoblob. In this way, you can create a hidden user-driven file system inside a container.
It is hidden because it is impossible to distinguish between random container data and random cryptoblob data, and it is impossible to determine the location of written cryptoblobs without knowing the positions and keys.
Containers do not contain any headers, all data about cryptoblob locations must be stored separately by the user.
The location of the start of the cryptoblob in the container is user-defined, and the location of the start and end positions of the cryptoblob must be stored by the user separately from the container. This is why this "file system" is called a user-driven file system.
Container structure (as an example):
+—————————————+ Position 0
| |
| Random data |
| |
+—————————————+ Cryptoblob1 initial position
| |
| Cryptoblob1 |
| |
+—————————————+ Cryptoblob1 final position
| |
| Random data |
| |
+—————————————+ Cryptoblob2 initial position
| |
| |
| Cryptoblob2 |
| |
| |
+—————————————+ Cryptoblob2 final position
| Random data |
+—————————————+
Tradeoffs and limitations
tirddoes not support public-key cryptography.tirddoes not support file compression.tirddoes not support ASCII armored output.tirddoes not support Reed–Solomon error correction.tirddoes not support splitting the output into chunks.tirddoes not support low-level device reading and writing when used on MS Windows (devices cannot be used as keyfiles, cannot be overwritten, cannot be encrypted or hidden).tirddoes not provide a graphical user interface.tirddoes not provide a password generator.tirdcan only encrypt one file per iteration. Encryption of directories and multiple files is not supported.tirddoes not fake file timestamps (atime, mtime, ctime).tirdencryption speed is not very fast: up to 180 MiB/s (in my tests).
Warnings
- ⚠️ The author is not a cryptographer.
- ⚠️
tirdhas not been independently audited. - ⚠️
tirdprobably won't help much when used in a compromised environment. - ⚠️
tirdprobably won't help much when used with short and predictable keys. - ⚠️ Sensitive data may leak into the swap space.
- ⚠️
tirddoes not erase sensitive data from memory after use. - ⚠️
tirdalways releases unverified plaintext (violates The Cryptographic Doom Principle). - ⚠️
tirddoes not sort digests of keyfiles and passphrases in constant time. - ⚠️ Overwriting file contents does not mean securely destroying the data on the media.
- ⚠️ Development is not complete, there may be backward compatibility issues in the future.
Usage
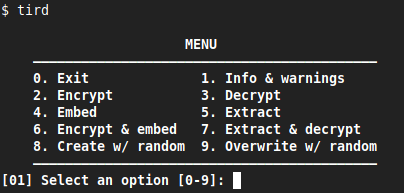
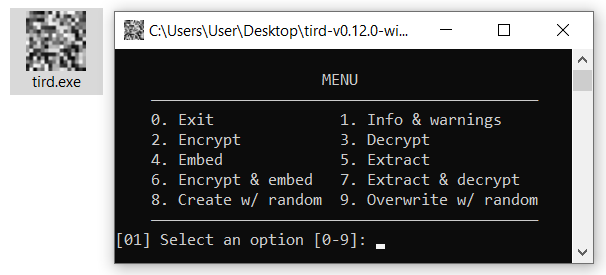
You don't need to remember command line options to use tird.
Just start tird, select a menu option, and then answer the questions that tird will ask:
$ tird
Debug
Start tird with the option --debug or -d to look under the hood while the program is running:
$ tird -d
Enabling debug messages additionally shows:
- opening and closing file descriptors;
- real paths to opened files;
- moving file pointers using the seek() method;
- salts, passphrases, digests, keys, nonces, tags;
- some other info.
Tutorial
See here.
Requirements
- Python >= 3.6
- PyNaCl >= 1.2.0 (provides
Argon2) - PyCryptodomex >= 3.6.2 (provides
ChaCha20)
Install
Install python3 and python3-pip (or python-pip), then run
$ pip install tird
Standalone executables (made with PyInstaller) are also available (see Releases).
TODO
Write documentation:
- Features;
- User guide;
- Specification;
- Design rationale.
Feedback
Feel free to post any questions, feedback or criticisms to the Discussions.
License
This project is licensed under the terms of the Creative Commons Zero v1.0 Universal License (Public Domain Dedication).
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.